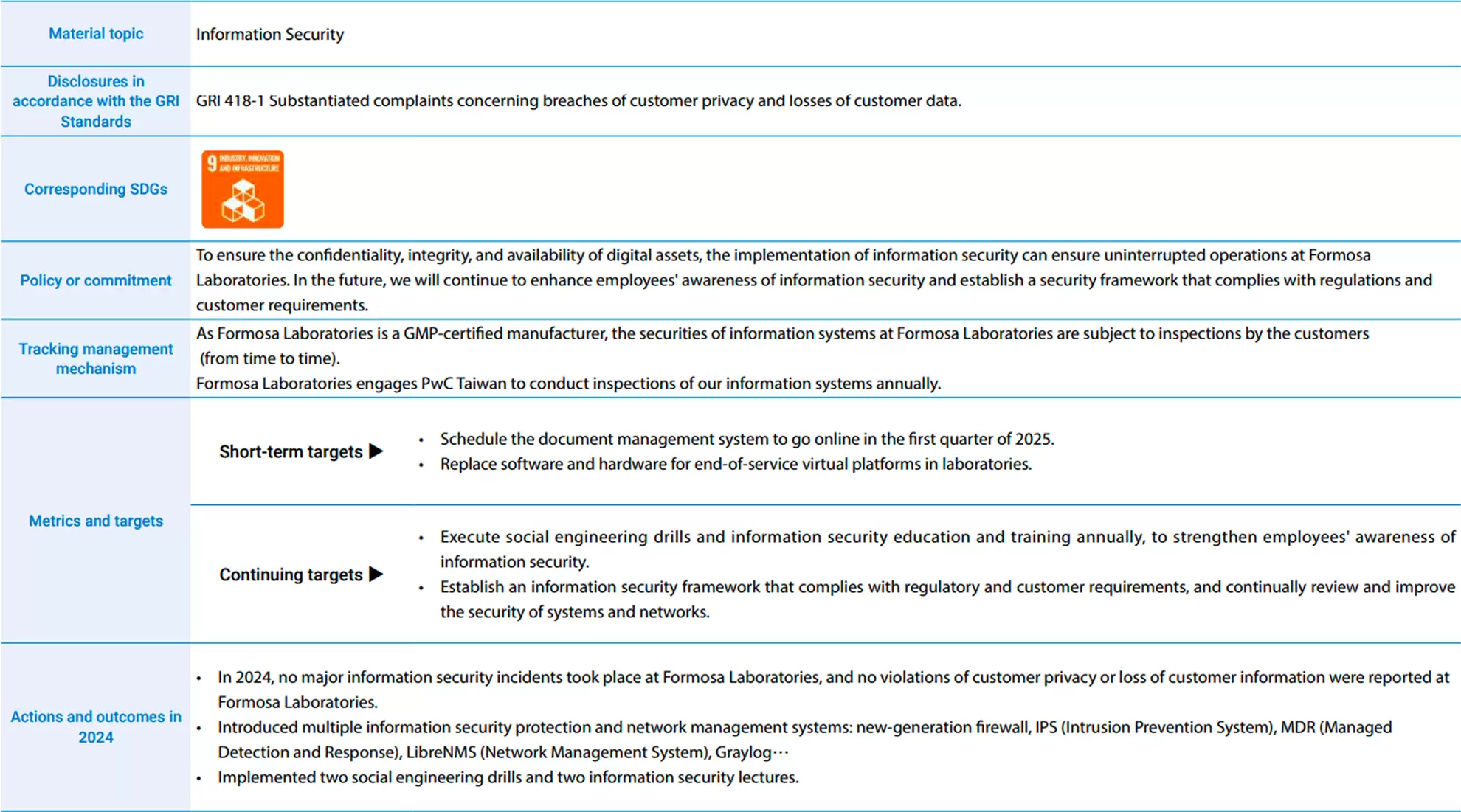
Management of material topic“Information Security”at Formosa Laboratories in 2024
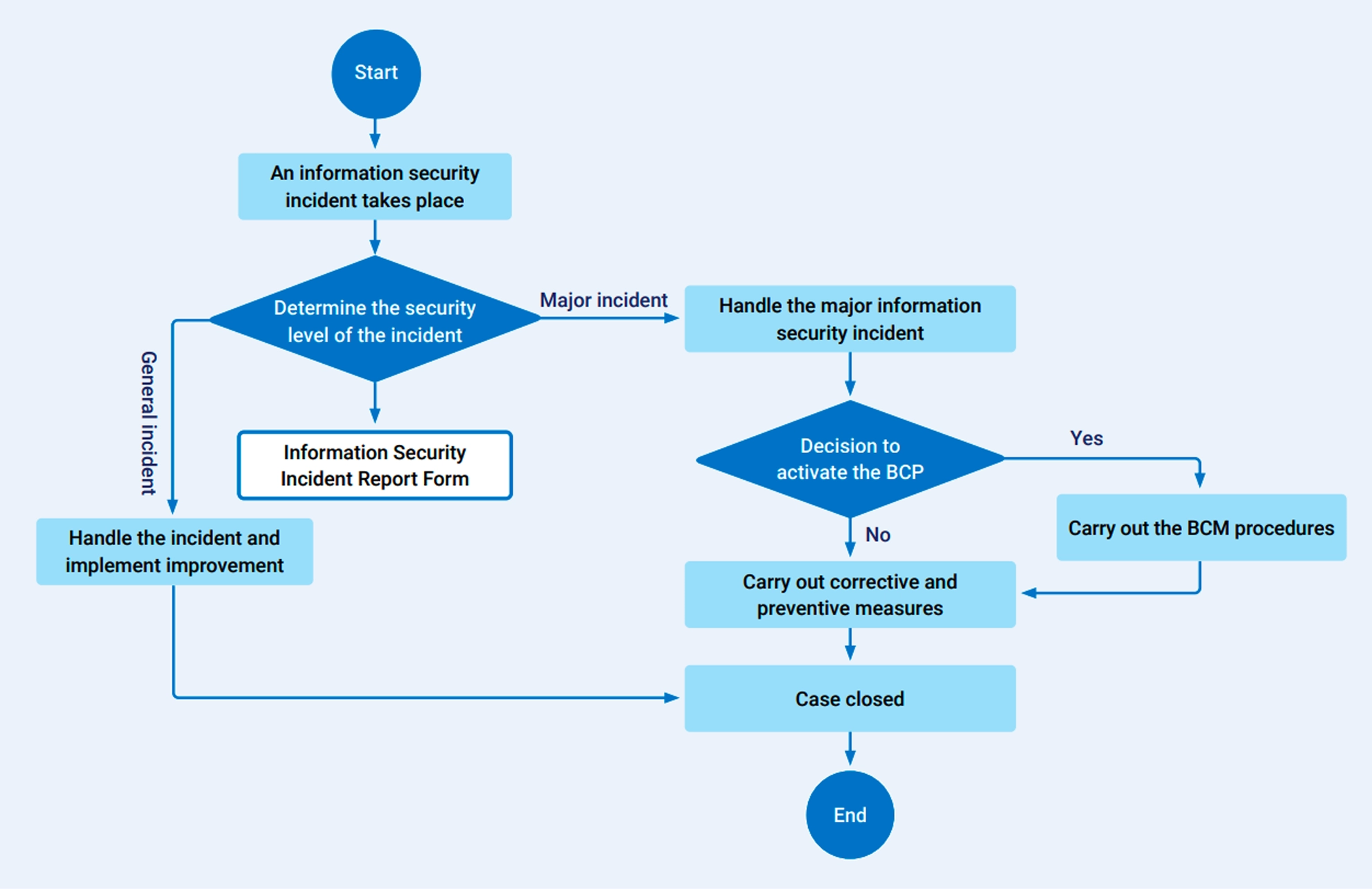
The Company is responsible for reviewing the information security governance policies of each unit and supervising the operation of information security management in order to enhance information security management. It is expected to construct a comprehensive information security protection mechanism and enhance the good information security awareness of colleagues through the management, planning, supervision, and promotion of professional information security units.
The Information Departmentis responsible for coordinating, managing, and supervising information security operations, which mainly cover the relevant information services provided by the department and the needs of other departments in the Company. We regularly conduct vulnerability scans, effectiveness checks of protective systems, and other related security testing tasks. We regularly assess information security risks and report to the information supervisor, as well as provide relevant security awareness and educational training courses. Through the operation of the Information Department and the implementation of security policies, we provide a secure and safe information security environment to ensure the information security of all company services.
Formosa Laboratories Protection of software and hardware equipment and data measures for information security
- Computer Room : The physical servers and related equipment used for the Company's infrastructure information system platform are all housed in a computer room with access control. Only authorized personnel and administrators are allowed entry.
- Hardware : The Company's servers, network equipment, and other hardware are designed with backup fault tolerance and clustering to ensure high availability of the system and hardware equipment.
- Storage Equipment : The Company utilizes physical equipment for data storage and backup, complemented by designs such as disk arrays and redundancy, to improve data protection and availability.
- Firewall : The Company has installed network security devices that can block different networks, preventing external unauthorized users from intentionally damaging, attacking, or tampering with the system and data to ensure their integrity.
- Intrusion Detection and Defense System : The Company identifies attack behaviors and system vulnerabilities based on the built-in feature database, providing administrators with early warning, evidence collection, and recording, as well as proactive response.
- All company computers must have antivirus software installed.
- The computer system must have account and password control, and the password must be regularly updated.
- The IT system is equipped with a UPS uninterruptible power supply system to prevent damage caused by power outages.
- Employees working remotely need to connect to the Company through a VPN.
- Performing system backups and offsite backups every day.
- Regularly conducting disaster recovery drills.
- Screen Protection Program : The Company has set up a system that automatically locks the workstation when the user leaves the seat or the computer is not in operation for a period of time. To unlock the computer, the user must enter their username and password, forcing them to establish a new access period for the control system.
- It is recommended that all personal computers be turned off after work to save energy, reduce carbon emissions, and minimize the risk of unauthorized access.
To strengthen information security management as outlined in the Information Security Policy, the Information Technology Department is responsible for coordinating and managing all security-related activities. This includes regularly conducting vulnerability scans, checking the effectiveness of protection systems, performing related tests, and assessing information security risks, which are then reported to the IT manager. Additionally, Formosa Laboratories conducts internal security training for employees annually and organizes security drills for specific departments, such as email social engineering exercises and remote recovery simulations.
In 2024, we conducted two social engineering drills and hosted two information security-themed lectures. Additionally, the videos from these lectures were used as required training courses for employees to continually enhance their awareness of information security.
As Formosa Laboratories is a GMP-certified manufacturer, we conduct information security inspections in strict accordance with the cGMP system. For example, Formosa Laboratories has implemented a comprehensive training program for production automation, office automation, partial automated control, quality management, research and development, and injectables. Additionally, Formosa Laboratories is subject to factory inspections conducted by the US FDA and TFDA every year, as well as periodic inspections of our information security systems by PwC Taiwan annually, and we are inspected by our customers approximately 30 to 40 times each year.

▼Information security measures and key digital technology programs in 2024
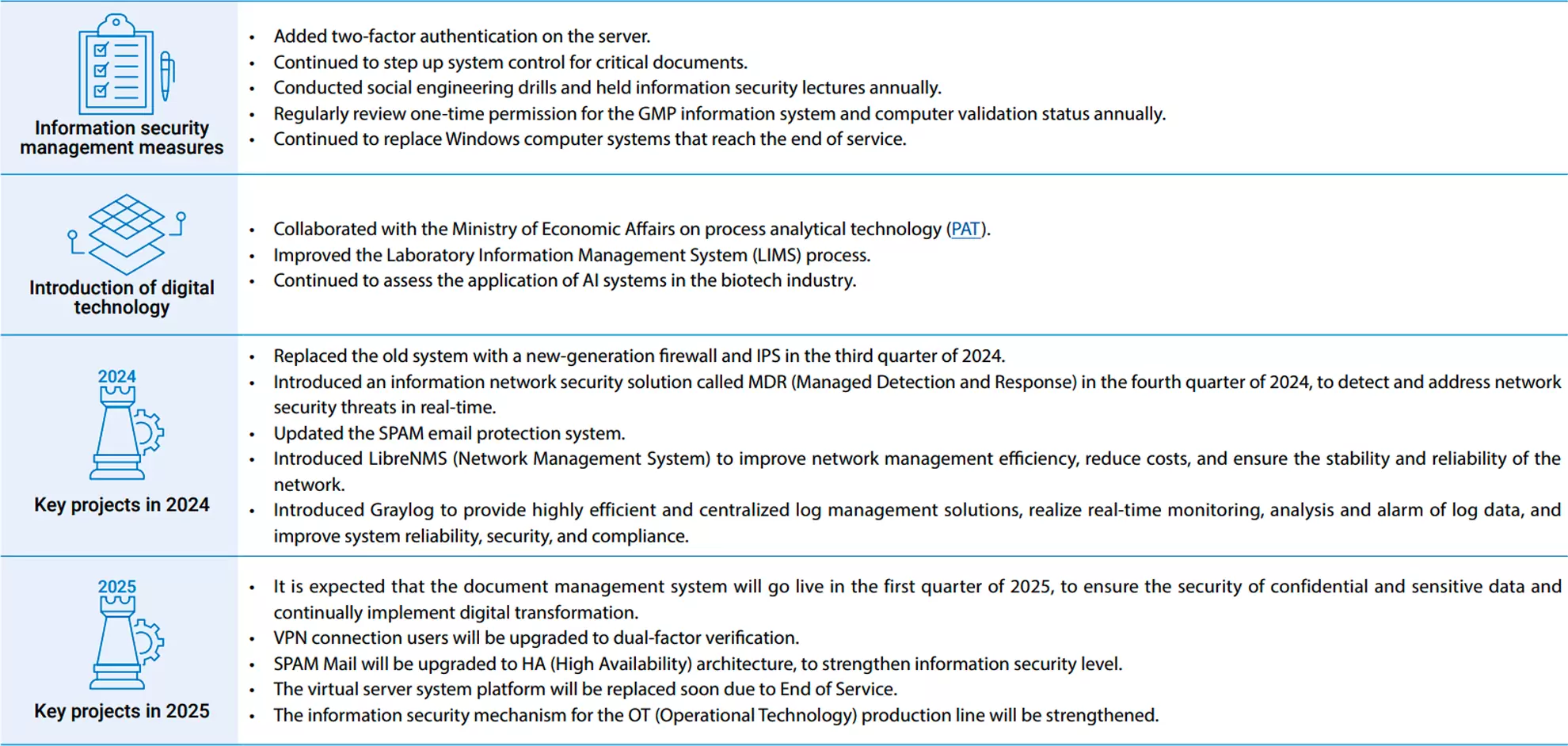
▼Information security measures and key digital technology programs in 2024